Unknown traffic bigger security threat than social media
By Gabey Goh May 28, 2013
- Social media-based threats only account for less than 1% of the threat logs in study
- Higher risk of malware infiltration deeper inside networks via unknown traffic masking C&C-type attacks
 IT may be taking the lion’s share of the airwaves right now, but the biggest threat to enterprise security isn’t employee usage of Facebook or YouTube – it’s hackers digging deeper into the corporate network.
IT may be taking the lion’s share of the airwaves right now, but the biggest threat to enterprise security isn’t employee usage of Facebook or YouTube – it’s hackers digging deeper into the corporate network.
According to findings from Palo Alto Networks’ latest Application Usage and Threat Report, applications everyone ignores were used heavily to mask malware activity. These include file transfer protocol (FTP), virtual private network (VPN) and Secure Sockets Layer (SSL) applications.
The report gathered data from 774 networks across 16 countries, across 2.3 petabytes of bandwidth detecting a total of 1,244 unique threats, with 44 million threat logs observed, the company said.
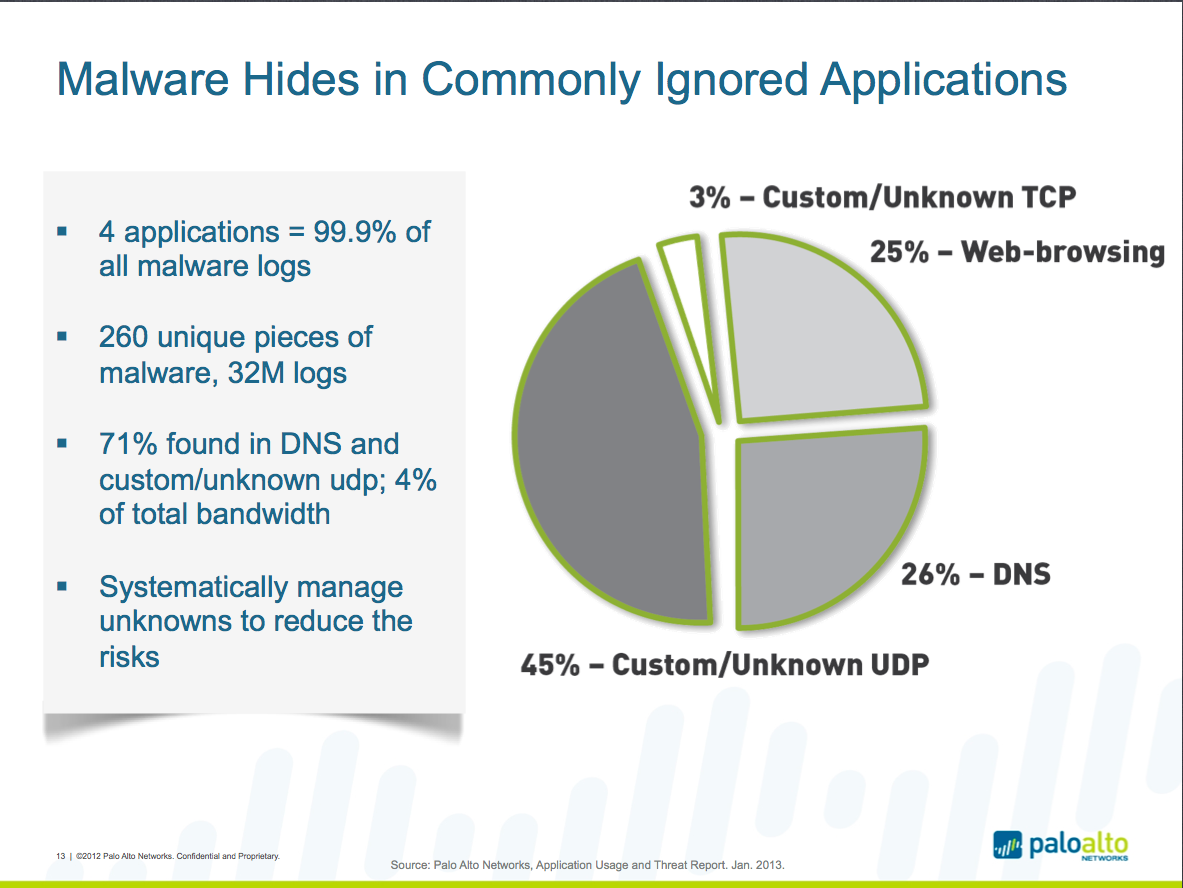
Four applications were responsible for 99.99% of the malware logs observed while 71% were found in custom/ unknown traffic and the Domain Name System (DNS). In addition, nine applications were responsible for 98% of all exploit logs observed, with seven of them being business applications.
In contrast, common sharing applications such as Facebook or DropBox made up 24% of the applications, 27% of the bandwidth used and less than 1% of the threat logs observed.
Out of the 27% of bandwidth used by common applications, YouTube only accounted for 7% while bitTorrent accounted for 4%; and 9% of bandwidth was used by file-sharing sites.
According to Palo Alto Networks, common concerns surrounding the use of common sharing applications include productivity loss from 'watching' or 'posting', regulatory or copyright violations, loss of confidential data, downloads infected with malware and the enticement to 'click here' being easily achieved.
 Kelly Brazil (pic), director of systems engineering, Asia Pacific, at Palo Alto Networks, said that while it is important to be diligent about social media and file-sharing applications, companies must also be aware that other parts of their network are susceptible to attacks.
Kelly Brazil (pic), director of systems engineering, Asia Pacific, at Palo Alto Networks, said that while it is important to be diligent about social media and file-sharing applications, companies must also be aware that other parts of their network are susceptible to attacks.
“This is where attacks are happening, deeper in the network on a more granular level. So the key for organisations is to segment their networks and to separate users from applications, not giving them access to every one,” he said.
Brazil also pointed to another finding of the report, which showed that 71% of malware activity was found in custom or unknown traffic, especially command and control (C&C) traffic, which would give attackers access to the entire network.
“What that means is that malware writers are writing their own protocols over TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) that doesn’t conform to any existing application. Traditional security devices don’t know what to do with the traffic and so they just let it in,” he said.
The report also found that 26% of C&C-type attacks came from the DNS, which Brazil said was a growing popular method.
“It’s easy to exploit in a way but the nice thing about DNS though is that gives us a way to identify C&C attacks. You can actually use DNS traffic to identify malware in a network,” he said.
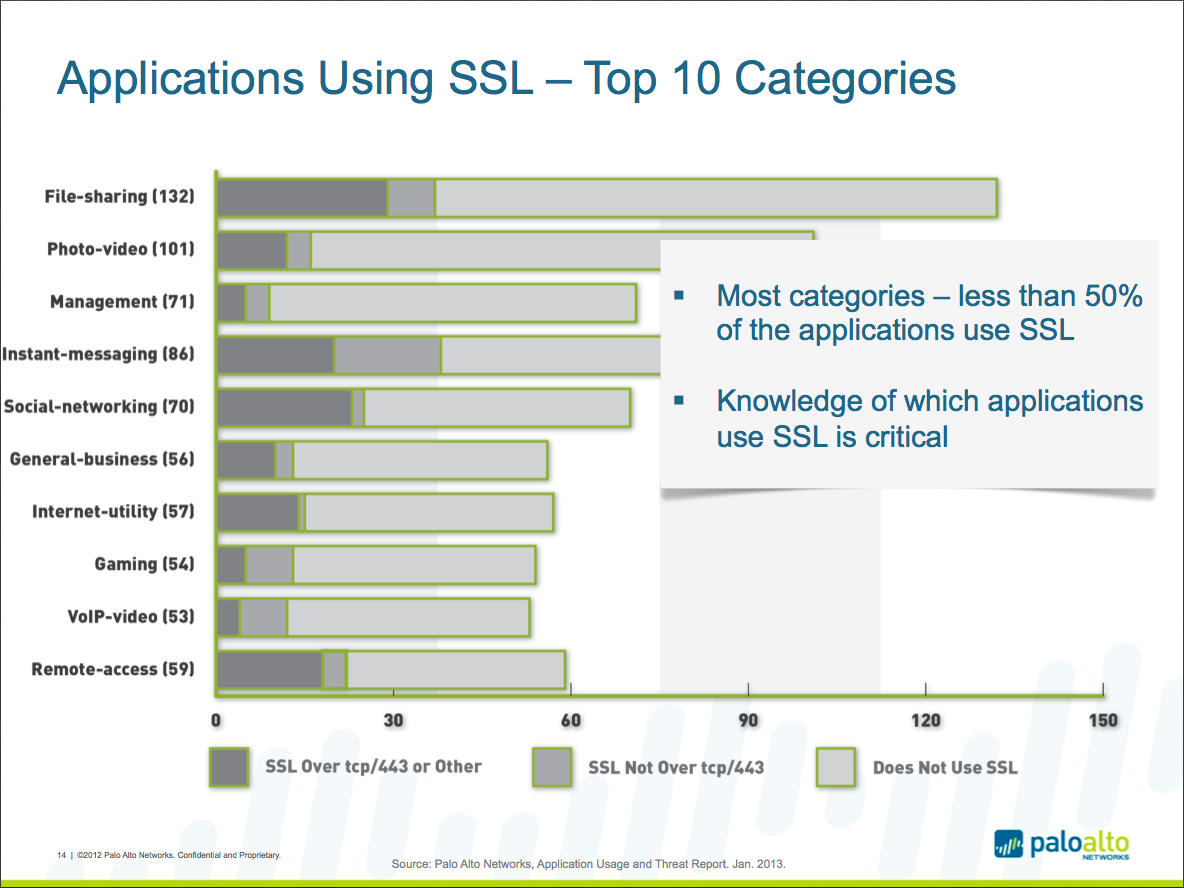
Another worrying threat lies in the SSL traffic that runs through a network, with Brazil noting that it is harder to differentiate between what is safe or harmful as the data is encrypted.
“And when you do decrypt the data, you find that it is a goldmine for C&C traffic that would compromise other parts of the network. Some applications may be using non-standard SSL ports or even rewriting the SSL handshake,” he said.
“It’s becoming more and more critical for enterprises to understand SSL traffic, which almost 50% of all applications use. Traditional security measures are more port-based so they do miss a lot of these more evasive applications,” he added.
According to Brazil, the network security company subscribes to a “positive enforcement model” for securing enterprise networks.
“It’s about allowing the things you want and denying everything else. It is also about bringing back what the firewall was supposed to do,” he said.
Brazil said that firewalls were originally built to protect networks from malicious traffic; however, with the advent of applications that can evade such measures, that control is no longer available.
“In the past, security was focused on protecting the perimeter of a corporate network. However with the rise of mobile devices and remote access to applications, it is important to not just protect the perimeter but to also bring security measures deeper into the network, segmenting the network even in virtualised settings,” he said.
The company’s 'next-generation firewall' is intended to address the changing threat landscape and is augmented by tools such as App-ID for application classification; User-ID for user identification and authentication; and GlobalProtect which extends firewall-based policies to remote devices outside the corporate network.
Another area covered by the company is the tracking of content traffic, via its Content-ID tool which combines a real-time threat prevention engine with a comprehensive URL database and elements of application identification to limit unauthorised data and file transfers.
Another security solution offered by Palo Alto is WildFire, which provides the ability to identify malicious behaviours in executable files by running them in a virtual environment and observing their behaviours.
“So this is the key here. Being able to scan for vulnerabilities and malware that already have signatures tied to it is one thing, but unknown threats is what we at Palo Alto refer to as modern malware,” said Brazil.
He said such unknown threats are highly associated with Advanced Persistent Threats (APTs), a cybercrime category directed at business and political targets, and typically form the first stage of an attack.


