Shadow IT: 80% of employees use unapproved apps at work
By Digital News Asia December 11, 2013
- IT employees are even bigger culprits than their business counterparts
- Office 365 the top unapproved app; followed by Zoho, LinkedIn and Facebook
 A SURVEY of more than 600 IT and line of business (LOB) decision-makers or influencers in North America, the United Kingdom, Australia and New Zealand saw more than 80% admitting to using non-approved SaaS (Software-as-a-Service) applications in their jobs.
A SURVEY of more than 600 IT and line of business (LOB) decision-makers or influencers in North America, the United Kingdom, Australia and New Zealand saw more than 80% admitting to using non-approved SaaS (Software-as-a-Service) applications in their jobs.
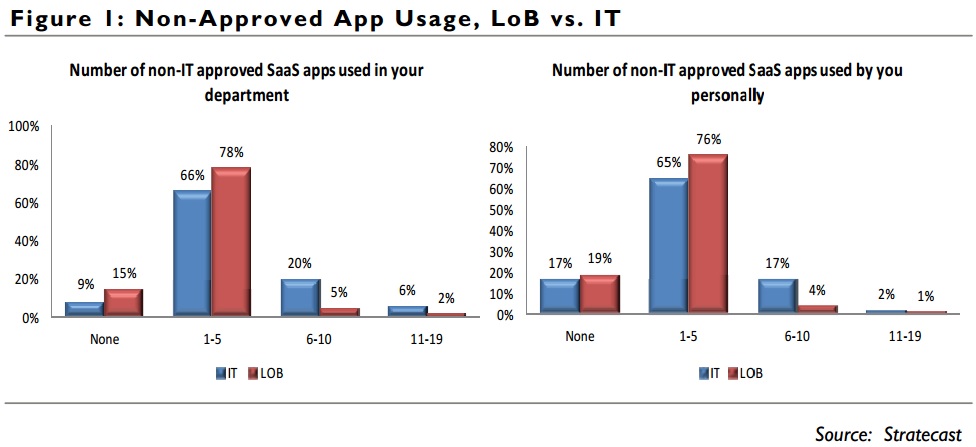
Furthermore, IT employees use a higher number of non-approved SaaS applications than other company employees, security solutions vendor McAfee said in a statement.
The study was conducted by Stratecast (a division of Frost & Sullivan). Two-thirds of the employees surveyed came from companies with 1,000-10,000 employees, and one-third from companies with more than 10,000.
These SaaS applications are also referred to as ‘Shadow IT,’ which is broadly defined as the use of technology solutions within an organisation that have not been approved by the IT department or obtained according to IT policies.
Frost & Sullivan estimates that the overall SaaS market in North America alone will grow at a 16% CAGR (compound annual growth rate), reaching a market value of US$23.5 billion by 2017.
The cloud also makes it relatively easy for employees to acquire and deploy SaaS applications without involving the IT department.
As a result, many applications are used by corporate employees and others (such as contractors or business partners) without the participation or approval of the corporate IT department, McAfee said.
Key findings:
- More than 80% of survey respondents admit to using non-approved SaaS applications in their jobs;
- Nearly 35% of all SaaS applications used within the enterprise are non-approved, contributing to Shadow IT;
- Microsoft Office 365 is the top unapproved SaaS application (9% of respondents), followed closely by Zoho (8%), LinkedIn (7%) and Facebook (7%);
- On average, 15% of users have experienced a security, access, or liability event while using SaaS;
- IT professionals use Shadow IT more than business users (81% of LOB users, and 83% of IT users); and
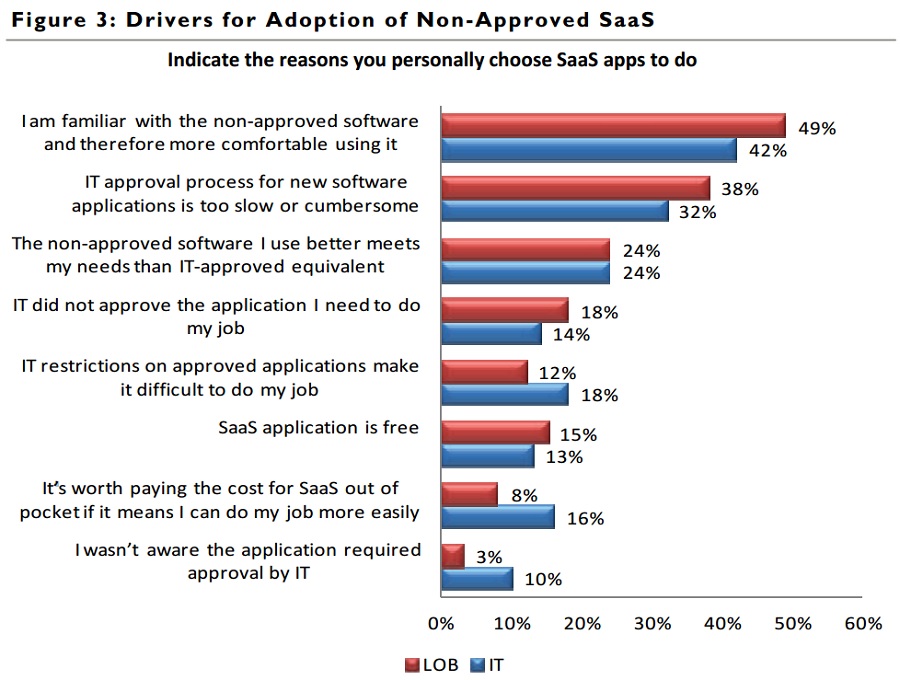
- 39% of IT respondents use unauthorised SaaS because “it allows me to bypass IT processes,” while 18% agreed that IT restrictions “make it difficult to do my job.”
“There are risks associated with non-sanctioned SaaS subscriptions infiltrating the corporation, particularly related to security, compliance, and availability,” said Lynda Stadtmueller, programme director of the cloud computing analysis service within Stratecast.
“Without appropriate knowledge, non-technical employees may choose SaaS providers or configurations that do not measure up to corporate standards for data protection and encryption. They may not realise that their use of such applications may violate regulations concerning handling and storage of private customer data, leaving the company liable for breaches,” she added.
So what makes these employees act rogue and deploy non-approved applications? In many cases it is not malicious at all – in fact, they are trying to do their job better, or make it easier, McAfee said.
In a hypercompetitive global business environment, in which companies are looking to increase tight margins, employees are increasingly being measured on results – in some cases, with their jobs at risk. So they will do whatever it takes to meet their job objectives, which presumably contribute to the company’s own business objectives.
 “With over 80% of employees admitting to using non-approved SaaS in their jobs, businesses clearly need to protect themselves while still enabling access to applications that help employees be more productive,” said Pat Calhoun (pic), general manager of network security at McAfee.
“With over 80% of employees admitting to using non-approved SaaS in their jobs, businesses clearly need to protect themselves while still enabling access to applications that help employees be more productive,” said Pat Calhoun (pic), general manager of network security at McAfee.
“The best approach is to deploy solutions that transparently monitor SaaS applications (and other forms of web traffic) and uniformly apply enterprise policies, without restricting employees’ ability to do their jobs better.
“These not only enable secure access to SaaS applications, but can also encrypt sensitive information, prevent data loss, protect against malware, and enable IT to enforce acceptable usage policies,” he added.
To view a copy of the full report, click here.
Related stories:
‘Shadow IT’ a pall on Malaysian IT landscape: VMware survey
BYOD: Kill off those old IT policies, CIOs
Cloud use in SEA facing 'rogue cloud' challenge: Symantec
Malaysians are all for BYOD, but their IT depts aren't: Survey
BYOD security: Singaporean SME staff left to their own devices
80% of BYOD use goes unmanaged, says Ovum
For more technology news and the latest updates, follow @dnewsasia on Twitter or Like us on Facebook.


