Policy framework a must for security today: IDC
By Gabey Goh October 4, 2013
- Policy frameworks must be established to better enable IT security measures
- CIOs in Malaysia see security as priority area of investment in 2013: IDC research
 THE first step for any organisation seeking to better address security concerns is to establish a policy framework, which will underpin the work their IT departments embark on.
THE first step for any organisation seeking to better address security concerns is to establish a policy framework, which will underpin the work their IT departments embark on.
That was the view expressed by Mayur Sahni (pic), research manager of services at IDC Asia/Pacific, during a media briefing hosted by Juniper Networks in Kuala Lumpur.
“The key is to put in place a policy framework that is in line with the business objectives. Only then can you secure your traditional or third party IT stack,” he said.
The clarity and collaboration required from all management stakeholders, not just the chief executive officer (CIO), in creating said policies would result in an organisation that’s better equipped to handle the increasing complexities of a modern IT environment.
“If you don’t know what to do or why you are doing it, what the benefits will be then whatever you end up doing, the success will only be short-lived,” Mayur said.
According to research conducted by IDC, CIOs in Malaysia see security as a priority area of investment in 2013, with two in three believing that ‘Governance’ and ‘Policy Framework’ would be important issues in 2013 and beyond.
With security spend expected to accelerate drastically over the next few years, many challenges remain for CIOs. Citing IDC research, Mayur said that the top three areas of security concerns were virtualisation (22%), mobility (29%) and social networking sites (18%).
“Security strategy today for many companies is still mainly a product-based one, where CIOs buy specific solutions to address specific areas in the IT architecture. It is not a holistic-approach, which is needed today to tie everything together due to the increasing complexity of the modern IT environment,” he added.
Mayur outlined five steps organisations should embark on to ensure a sound approach to security:
- Institute a security and risk management programme;
- Manage the complexity and risk which come with an extended enterprise;
- Protect critical information assets;
- Establish a life-cycle approach to data; and
- Develop pervasive cyber resilience.
When asked if the heightened focus on security stemmed from the acknowledgement of its importance for the long-term, or was merely a reaction to the public outing of nation-state surveillance programmes such as PRISM and other high-profile breaches, Mayur said that it was both.
“However my worry is that a knee-jerk reaction of companies may result in half-hearted attempts, where they just comply and do the minimum required, as it won’t solve the problem and long-term pain.
“Now is a good time to regroup and find out what’s needed for the long-term to minimise security risks,” he said.
Mayur said that to date, only about 74 companies in Malaysia have attained the Information Security Management System (ISMS) Certification (MS/IEC ISO 27001:2007), a list that includes Malaysia Airlines.
He said that Malaysia’s maturity as a market is not on par with Singapore, but is not as low as others in the region. However, as the plan to become a developed nation goes forward and all the pieces come together, there is a need to have a strong backbone for how IT security is to be addressed.
He added that in Malaysia, adherence to internal policies is very low in BYOD (bring your own device) environments, and adoption of the trend is generally lower due to security fears.
“Most IT departments have a clear idea of how to address concerns but can’t due to internal processes. From a security point of view, you need to know what the corporate policies are and only then can you proceed,” Mayur said.
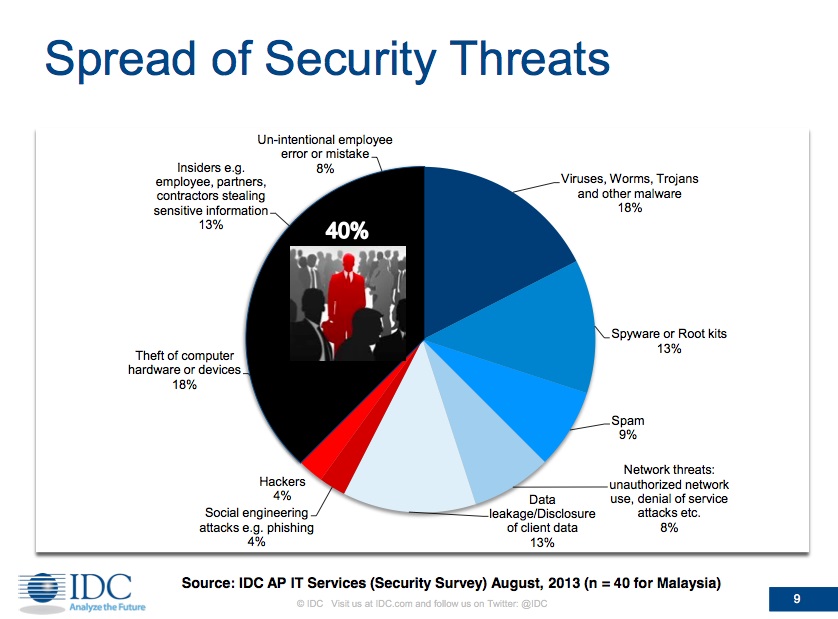
In addition, with employees being the source of just under 40% of threats, from insider data theft (13%), computer hardware or devices theft (18%) to unintentional employee error or mistake (8%); an effective and enforceable security policy framework becomes all the more pertinent (see chart below).
“The thing is, until there is regulation or compliance serving as drivers, the adherence to security is not there,” Mayur said.
He added that any approach toward security needs to consider securing not just the network or the data, but all layers of the stack and not just one.
As the IT stack changes, and becomes more external with the increasing deployment of applications to mobile endpoints, the exposure of corporate networks to security risk increases exponentially.
“There is a need to comprehend security more realistically and there needs to be a long-term security risk management programme with full C-level support. You can tell a lot about an organisation by the way its IT is run.
“There is significant evidence in companies, showing that those with an IT security strategy that moves in line with the business are better positioned to compete and deliver real value,” he added.
When asked how ready companies are in terms of truly addressing security concerns, Mayur said that how everything finally pans out depends on the organisation’s propensity to invest in the area.
“Outcomes are determined by the appetite to address the issues and what the company’s acceptable level of risk is in designing its security strategy,” he said.
Up Next: Juniper Networks on using deception for protection
Related Stories:
CyberArk unveils Master Policy, new approach to privileged account security
Security as a business enabler, not a bottleneck
Big data approach can help shore up cyber-defence: RSA
Security no longer about ‘no,’ but ‘know’
How to reduce policy accumulation and improve security
Cyber-war: Time for our agencies to step up
For more technology news and the latest updates, follow @dnewsasia on Twitter or Like us on Facebook.


