‘Hackers’ – tech reality finally catches up with Hollywood?
By A. Asohan October 11, 2012
- A so-so movie from 1995 has actually predicted the future more accurately than serious SF dramas
- Hollywood may have focused more on coolness and glitz, but the Hackers reality is beginning to come true
 IT has been some time, but the last time I watched the 1995 movie Hackers, I remember sniggering at how it got the technology all wrong. Hollywood – which still believed that electrical overloads and lightning strikes could confer sentience on anything more complex than a Babbage Difference Engine – just did not understand computers.
IT has been some time, but the last time I watched the 1995 movie Hackers, I remember sniggering at how it got the technology all wrong. Hollywood – which still believed that electrical overloads and lightning strikes could confer sentience on anything more complex than a Babbage Difference Engine – just did not understand computers.
Well, it turns out that Hackers was more accurate in predicting the future than Stanley Kubrick’s 2001: A Space Odyssey (1968). There are no flights to the moon, but many of the seemingly ridiculous things that the young hackers did in the movie are not only possible, but inevitable.
Or at least, that’s what Don Bailey, founder of Capitol Hill Consultants, argued at the on-going Hack In The Box Security Conference (HITBSecConf2012) in Kuala Lumpur. “Hackers predicted many aspects of what Internet security would be like, 17 years later,” he told a rapt audience.
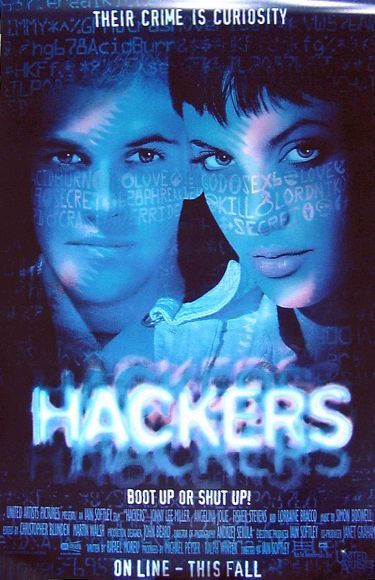
The movie, about a group of high-school hackers who run afoul of the US Secret Service, starred Jonny Lee Miller (Dade ‘Zero Cool’ Murphy) and Angelina Jolie (Kate Ácid Burn’Libby), before she got all Hollywood-glam, as well as Fisher Stevens, who played the villain who had created an apocalyptic computer virus.
''It was 1995 and the Internet was lame,” said Bailey. Which is perhaps why Hollywood decided to gloss over the technological realities of the time and instead focus on pace and glitz.
Noting that it was the 10th anniversary of the HITB series of security conferences, Bailey said that it was a good time to look back at technology back then. “I think the movie is a perfect way of taking a step back and see how we view the Internet, and how we view ourselves [as hackers].”
Bailey looked at many of the hacks and techniques used in the movie, and how they are actually more realistic today, while discussing how contemporary technology actually allows some of the more far-out hacks to be performed.
When it comes to the former, he noted how the password dumps and kernel hacking used in Hackers have become bona fide methods of intrusion, the latter especially when it comes to Apple’s iOS platform. “Hacking kernels was a foreign idea at the time,” he said.
And while the film-makers must included them then because they just looked cooler, Bailey noted, ''ánother interesting is they were all using Macs – not something you’d have associated with hackers back then.”
In the movie, the kids hack into sprinkler systems, a television network, the electrical grid and even traffic light managements systems, many times remotely. “Hackers was into machine-to-machine (M2M) networks before it became a reality,” he said, noting the increasing popularity of smart homes and smart buildings, in which so many functions are controlled by computer systems that can be accessed remotely.
As for remote hacking, Bailey said that everything is going to be cellular enabled."We’re beginning to link our physical world to our technology world in ways we never thought about 10 years ago.”
He said technology was now being used to alert farmers on when foals were about to be born so that they can assist in the birth, to tracking cows.
And he noted that with the rise of technologies such as Zigbee and industrial systems getting on the grid, from oil tankers to factories, even the prospect of hacking to create a worldwide ecological disaster – the climax of the movie’s plot – which would have produced polite coughs of derision in 1995, is now a reality.
The blurring of the border between the real world and the virtual world is creating new sets of worrying vulnerabilities. “Security risks occur when people don’t realize the implications of the technologies they employ,” said Bailey.
“Real hackers hack everything, from your cellphone to your cow. And they are extremely patient. It doesn’t have to be a complex hack – sometimes hacking just means understanding the technologies being used well enough to execute the simplest hack.”
In fact, Bailey argued that there was a need for the hacker subculture of people with nothing better to do sitting in front of their laptops and testing this and that, “because we need to know what security risks there are out there.”
Finally, when Digital News Asia (DNA) suggested another fiction-turns-to-reality aspect of Hackers, Bailey agreed: “The movie was the first to make geeks look cool.”
HITB is celebrating the 10th anniversary of its security conference by bringing back on stage 42 of its most popular speakers from the past decade, including hacker legend John ‘Captain Crunch’ Draper; leading info-security expert Mikko Hypponen, the chief research officer at F-Secure; Lucas Adamski, director of security engineering at Mozilla; and the iOS Dream Team.
HITBSecConf2012 (or HITB2012KUL) includes a number of side events, such as the Capture The Flag network hacking challenge; the HackWEEKDAY 36-hour hackathon which made its first appearance at last year’s conference; and the HITB CommSec Village, an area that would be dedicated to highlighting various security related projects from the open source community and from various hackerspaces.
In addition, Google has announced Pwnium 2 - putting a total of US$2 million in rewards on the table for anyone who can find bugs in its browser, exploit them, and tell Google’s security team the details of their techniques.
There will also be a charity auction just before the closing ceremony on Oct 11, with all proceeds going to the Needy Cancer Patient Fund managed by Mount Miriam Cancer Hospital, a hospital located in the northern Malaysian island of Penang whose goal is to make treatment affordable to all cancer patients.
For more information on HITBSecConf2012, go to http://conference.hitb.org/hitbsecconf2012kul/ or follow the @hitbsecconf Twitter account for up-to-the-minute updates. The hashtag for the event is #HITB2012KUL.
DNA is amongst the supporting media for the event. For full coverage, click here. For another inspiring story about hackers, check out our three-part history of Hack In The Box.


