Malaysia’s domain registrar MYNIC breached … again
By Edwin Yapp October 11, 2013
- MYNIC’s DNS compromised again; Google Malaysia targeted by a group known as Madleets
- DNSSEC needs to be implemented immediately; website owners also need to take issue more seriously
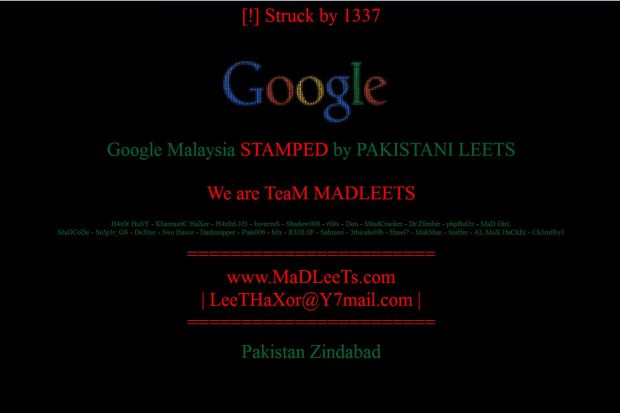
THE Malaysian registrar for the ‘.my’ top level domain MYNIC Bhd may have failed to prevent an attempt to breach its Domain Name Server (DNS) by a hacker group known as Madleets, which had led Google Malaysia to experience, for a second time this year, a re-direction of its http://www.google.com.my/ and http://www.google.my/ search pages late on Oct 10.
News of this was first reported this morning (Oct 11) by TechCrunch, which unfortunately reported that Google’s Malaysian website has been ‘hacked and replaced’ with a splash screen giving credit to a group called ‘Team Madleets,’ and that links on the page also lead to its Facebook page.
This is the second time legitimate websites in Malaysia were re-directed in such a ’DNS hiijack’ this way. Digital News Asia (DNA) reported such an attack on July 1 which also affected Google Malaysia, along with domains owned by Dell Malaysia, Microsoft Malaysia, Skype Malaysia, Kaspersky Malaysia.
In that incident, search queries involving Malaysian domain names led visitors to temporary sites with a message from what appeared to be a hacker group protesting the treatment of Bangladeshi workers in the country.
MYNIC has confirmed its servers were compromised through a tweet on its official Twitter account as well as its website on Oct 11, saying “We can confirm there was unauthorised redirection of www.google.com.my and www.google.my to another IP address by a group which called themselves TeaM MADLEETS (sic).
“The problem was alerted [sic] in the early morning and MYNIC Computer Security Incident Response Team (CSIRT) immediately started to resolve the issue. The domain name www.google.com.my has been restored to their correct information at 7.10 am today and www.google.my is still resolving. At the moment, we are undertaking all necessary measures to monitor the situation and prevent further related issues.”
MYNIC initially did not respond to calls for further clarification and there were also no new updates on its website and Twitter accounts as at press time when this article was published at 7pm. However after the story went live, MYNIC reverted back at 8.20pm, denying that its servers had been compromised.
“Our findings show that the redirection is done through one of MYNIC Reseller’s account. We can assure the public that no customer’s content, password information and other personal information was affected by the redirect,” said Hasnul Fadhly Hasan, chief executive officer of MYNIC.
As the sole administrator for '.my' domain name in Malaysia, MYNIC is undertaking all necessary measures to monitor the situation and prevent further related issues. MYNIC is also looking forward to enhance its security system through comprehensive improvement, the national domain registrar said in a statement.
“Since the first incident on July 1, various security measures have taken place on MYNIC’s infrastructure and our records show that unauthorised access to the system no longer occurs... MYNIC’s next course of action is to immediately improve resellers’ security on account management,” Hasnul added.
Other governmental agencies such as the Malaysian Communications and Multimedia Commission (MCMC) and CyberSecurity Malaysia did not immediately respond to queries.
When contacted, Google Malaysia’s spokesman told Digital News Asia, “For a short period, some users visiting google.com.my were redirected to a different website; Google services for the google.com.my domain were not hacked. We've been in contact with the organisation responsible for managing this domain name and the issue should be resolved.”
Must be more vigilant
According to a security expert DNA spoke with, the kind of cyber-attack experienced by Google Malaysia, both on July 1 and Oct 11, is known as ‘DNS poisoning.’
Suresh Ramasamy, a security expert with Hack In The Box (HITB), noted that DNS poisoning typically involves a hacker gaining access to MYNIC’s servers and changing the DNS records of a website – in this case Google Malaysia’s – in a bid to point it to other servers chosen by the hacker, thereby directing legitimate Google visitors to the Madleets page.
“At this point, it looks like a [DNS] cache poisoning issue, but then, there may be other reasons why the incident happened,” he said in an email.
Suresh said this kind of attack does not mean that Google search servers were in themselves hacked or compromised; it’s just that hackers had been able to gain access to the MYNIC’s servers, thereby controlling the flow of traffic away from Google to Madleets’ website.
“As you’ve highlighted, this is the second incident with MYNIC and in the case of a domain registrar [such as MYNIC], there are a few points of vulnerability,” he explained. “This includes issues from web-based registration and administration, right up to how the domains are populated and managed at the DNS [level].”
 Asked what must be done to prevent such incidents from happening again in the future, Suresh urged MYNIC to beef up its security protocols and to be far more vigilant in defending against attempts by hackers to compromise its DNS.
Asked what must be done to prevent such incidents from happening again in the future, Suresh urged MYNIC to beef up its security protocols and to be far more vigilant in defending against attempts by hackers to compromise its DNS.
“As a national organisation in charge of the DNS, it’s a heavy responsibility as there’s a high level of expectation on service availability.
“All one needs is a reason – be it name, fame, shame, money, reputation, or motivation – and any organisation can be targeted. [To my knowledge], MYNIC has also started implementing DNSSEC (which does help to resolve such issues), but from a quick check shows that DNSSEC isn’t enabled for the affected domain.
“That doesn’t prevent an organisation such as MYNIC from having the right level of readiness against such attacks,” he said. “And I would expect MYNIC to be able to deal with such threats judging by the fact that it has been through this before and also since it is an ISO 27001-certified organisation.”
ISO 27001 is an information security management certification handed out by the International Standards Organisation or ISO.
Suresh also said MYNIC needs to conduct active monitoring and have an effective close working relationship with all the relevant parties and their respective regulatory counterparts, which he said usually helps to resolve these type of issues more quickly.
Notwithstanding the responsibility on MYNIC, he also had warnings for website owners.
“Website owners need to start taking their DNS more seriously. Though it’s usually a ‘once-in-a-lifetime’ setup for most domains, DNS failure means complete blackout of their online presence.
“Proper zone planning, together with implementing considerations such as DNSSEC, helps to mitigate some of the commonly seen risks,” Suresh said.
Related Stories:
DNS poisoning: MYNIC admits servers compromised
Malaysian sites hit by DNS poisoning
Week in Review: Trust, security and standards, or lack thereof
DNS hijacking: Government needs to step in
For more technology news and the latest updates, follow @dnewsasia on Twitter or Like us on Facebook.


